After a massive data breach leaked the entire database of the Philippines’ Commission on Elections (COMELEC), every registered voter in the Philippines is now susceptible to fraud and other risks. While initial reports have downplayed the impact of the leak, Trend Micro investigations showed a huge number of sensitive personal identifiable information (PII)–including passport information and fingerprint data–were included in the data dump.
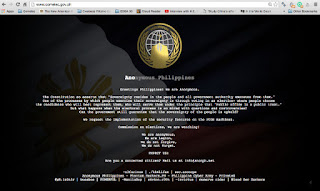
Following the defacement of the COMELEC website on March 27 by a hacker group, a second hacker group posted COMELEC’s entire database online. Within the day, they added three more mirror links where the database could be downloaded. With 55 million registered voters in the Philippines, this leak may turn out as the biggest government related data breach in history, surpassing the Office of Personnel Management (OPM) hack last 2015 that leaked PII, including fingerprints and social security numbers (SSN) of 20 million US citizens.
This incident has thus far caused the following:
· Tension and pressure on the upcoming election tension
· Exposure of website’s vulnerability to security
· Leak of personal data of overseas Filipino voters
According to Trend Micro’s research paper, Follow the Data: Dissecting Data Breaches and Debunking Myths, government agencies are the third biggest sector affected by data breach, followed by retail and financial industries. The recent security incidents highlighted the need for stronger security mindset and data classification among organizations and companies, given the possible impact of the breach to voters and people alike. This also brings to the fore the importance of having data protection officers that would be responsible for the legal requirements as well as securing all types of crown jewels or highly sensitive data of organizations.
It is important to instill a security mindset when dealing with important data, and companies should practice data classification to segregate data of varying sensitivity and applying appropriate protection to each category. End point solutions can protect also protect companies and organizations by detecting malicious files that are used as infiltration methods during data breaches.
If you’re interested to find out more on the incident and solutions, follow the link to the blogpost.
For the LATEST tech updates,
FOLLOW us on our Twitter
LIKE us on our FaceBook
SUBSCRIBE to us on our YouTube Channel!