Trend Micro’s CTO Raimund Genes once said, technology is a tool, and people put it to good or bad use. Cybercriminals have long been abusing legitimate online tools and services. Now, according to Trend Micro’s research, there’s another group that shares the same alarming levels of proficiency in exploiting cybersecurity tools to achieve their own purpose: terrorist groups.
Trend Micro’s report, Dark Motives Online: An Analysis of Overlapping Technologies Used by Cybercriminals and Terrorist Organizationsdiscusses the methodologies, services, and tools that cybercriminals and terrorists utilise to streamline their cause for followers to facilitate their activities easily. These include the following:
· How terrorists remain untraceable and anonymous
· Disseminating propaganda online
· Customized tools to aid in their guerrilla campaigns
According to Trend Micro, both cybercriminals and terrorists resort to using anonymizing programs such as TOR, and certain encryption tools found in the Deep Web to hide their identities. In comparison however, the way both parties disseminate information related to their agenda are different – with cybercriminals being more inclined to engage with their limited contacts and weigh on the online reputation of the individual.
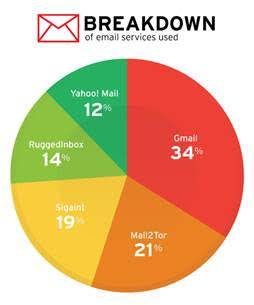
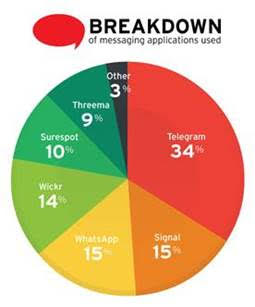
In addition, terrorists and cybercriminals have been known to use the same services such as Yahoo! Mail and Gmail in order to communicate, coordinate and share propaganda whereas for popular messaging applications such as Whatsapp and Telegram, it’s communication and coordination rather than for information theft or to spread malicious links. Telegram was found as the most favoured method of communication amongst terrorist groups, with 34% listing their contact information as a Telegram address. Other messaging applications such as Wickr, Surespot, Signal, and Threema accounted for the rest, along with Whatsapp and more.
For the LATEST tech updates,
FOLLOW us on our Twitter
LIKE us on our FaceBook
SUBSCRIBE to us on our YouTube Channel!