Recently recognized in the leader quadrant in Gartner 2017 Magic Quadrant for Web Application Firewalls, F5 Networks has launched its latest report: Threat Analysis: The Hunt for IoT – the Rise of Thingbots, which continues to track Telnet activity, and the progressions of Mirai, as well as Persirai (a new thingbot). Thingbots are botnets which are built exclusively from IoT devices, and F5’s research indicates that these “thingbots” are set to become the infrastructure for a future darknet. In essence, the report exposes how IoT devices have been, and will continue to be one of the most highly exploitable tools in the arsenals of cyber attackers.
Image: Internet of Things devices connect the world around us and power our lives, but make us more vulnerable to being hacked
Cybersecurity is hot on the menu at the moment, with the Singapore government recently introducing a new Cybersecurity Bill to provide a framework for the regulation of critical information infrastructure. This comes at a timely junction, with the effects of the recent WannaCry and Petya attacks still fresh in the minds of the public, especially with recent research estimating that cyber-attacks could potentially cost the global economy US$120 billion – thesame amount as Hurricane Katrina. Worse than economic damage, however, is the damage to a brand’s reputation, and the loss of customer’s trust.
Image: Countries where top 50 IP addresses reside
Image: Persirai-infected IP cameras and Command & Control servers, Asia, June 2017
As evidenced by the map above, cybersecurity will continue to remain a key concern in today’s ever connected world, driven by the rise of IoT. This will be the case especially as hackers find new ways to leverage unprotected devices to launch their cyber-attacks. The reality remains – our world of unsecured devices is the new playground for hackers; and according to F5 Networks’ latest report, this is not going to change (until IoT manufacturers are forced to secure these devices), as IoT devices are becoming the “cyberweapon delivery system of choice” by today’s botnet-building attackers.
Image: Historical view of IoT attack growth by quarter, January 2016 through June 2017
Some of the key insights:
· IoT attacks rose by 280%, attributed to the Mirai malware and its subsequent attacks (Image above)
· China, previously the top source country from which attacking activity originated, has dropped off significantly, contributing less than 1% of the total attack volume
· Instead, Spain has taken over as the leader in attacks, with 83% of attacks launched from a hosting provider network based there
· Hackers are building thingbots based on specific disclosed vulnerabilities in IoT devices, rather than having to find new exploits
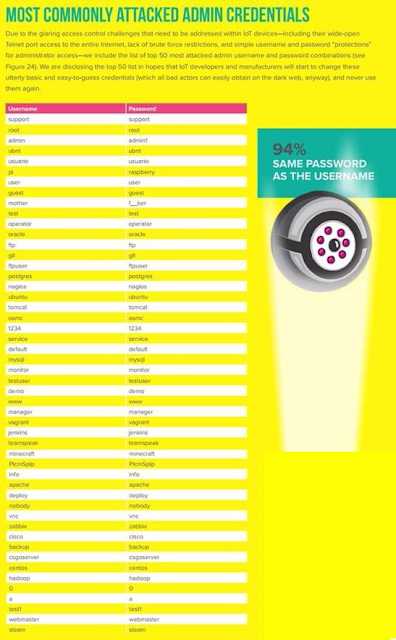
Image: Top 50 most attacked admin username and password combinations; 94% of respondents admit to using the same passwords as their usernames for logins
What does this mean for enterprises?
· Have a DDoS strategy ready at hand
· Ensure redundancy for critical services, and that they are prepared for downstream impact
· Implement credential stuffing solutions
· Train employees on the threat and vulnerability of IoT devices – the more aware they are of these threats, the less likely they are to become affected by the attacks
Threat Analysis: The Hunt for IoT – the Rise of Thingbots is the third volume of F5 Networks’ IoT reports, following the second volume Threat Analysis Report: The Hunt for IoT. To find out more on the subject, the full report is available here with further detail on global and market trends.
For the LATEST tech updates,
FOLLOW us on our Twitter
LIKE us on our FaceBook
SUBSCRIBE to us on our YouTube Channel!